The UAT Cyber Warfare Range (AKA "The Cave") is the main hub for network security, network engineering and technology forensic students at the University of Advancing Technology. All of our classes take place in this room, and we also host cyber security events in this collaborative space.
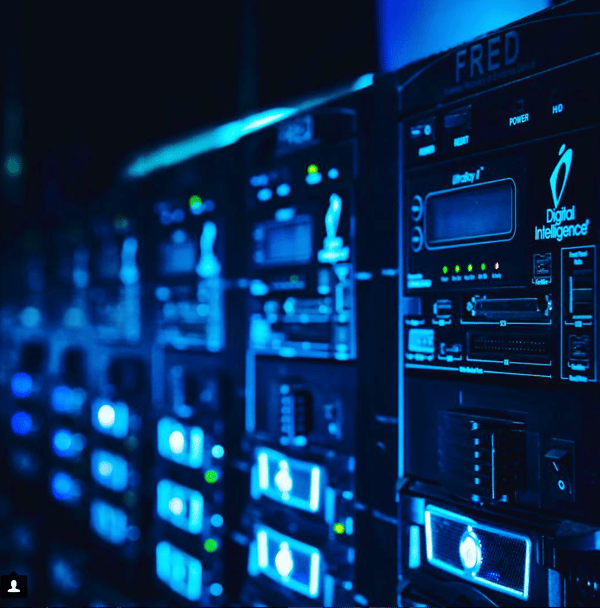
The room itself works differently from traditional classrooms because it was designed to promote hands-on learning. Students work off an isolated network and have access to Forensics Evidence Recovery Devices (FREDs).
In entry-level classes such as Foundations of Systems Administration, students build a virtual network composed of Windows Server 2016. In another class, I got a work order and had to complete the tasks on it by the deadline, just like in the real world. I used the cluster to make a network comprised of virtual machines, which helped me complete tasks such as setting up an active directory and giving different users different permissions.

In Computer Forensic Essentials, the professor gave us a hard drive image and tasked us with writing a case report. In order to accomplish this task, we utilized the FREDs. These devices enable students to image a flash drive or hard drive for forensics recovery software. One of the main focuses of the class is ensuring that evidence remains valid and useable in the court. The emphasis on validity is important because digital evidence can be easily tampered with.
But we don't use preserve evidence and data, we also document everything.
In forensics, correct documentation enables the examiner to adequately describe how the evidence was handled. Documentation also helps law enforcement and lawyers effectively present the evidence.
Many different moving pieces work together to help an enterprise network function. That's why it's so important to document what changes you make, so another person can use that document when they need to troubleshoot or use a reference.

Outside of classes, we also host events in the UAT Cyber Warfare Range. For example, the Information Security Organization holds weekly meetings in the Range, where students showcase what they are working on or explore topics together.
Jackson Nestler is the club president and a UAT Cyber Warfare Range intern. “We host two primary activities outside of our typical classes in The Cave: the Collegiate Cyber Defense Competition (CCDC) meets on Tuesdays at 6:30 pm to prepare for upcoming competitions, train and discuss strategy. And on Saturdays at 6 pm, we have our Information Security Organization (ISO), which is a casual meetup for students interested in learning real-world security applications, expanding on the knowledge that they receive in classrooms and meeting like minded peers. Right now, we’re working on bringing guest speakers to ISO as well," Nestler said.
To learn more about The Cave or our Cyber Security program, visit our website.