 Source: http://www.kahusecurity.com/
Source: http://www.kahusecurity.com/
It is a known fact that internet service providers and protection agencies for the government are monitoring metadata of every user that has an internet or cell connection to a device. Not only do they have this access, private companies are also doing the same to buy, sell, and use your metadata to advertise, predict buying habits, and in some cases telling your parents you are pregnant. This blog isn't a debate of privacy and tracking, but rather I want to show you two techniques in how normal people are confusing algorithms in order to make their metadata worthless to monitors, buyers, and sellers in both the private sector and government surveillance.
Algorithmic-frustrating Queries
 Source: http://www.coaa.co.uk/
Source: http://www.coaa.co.uk/
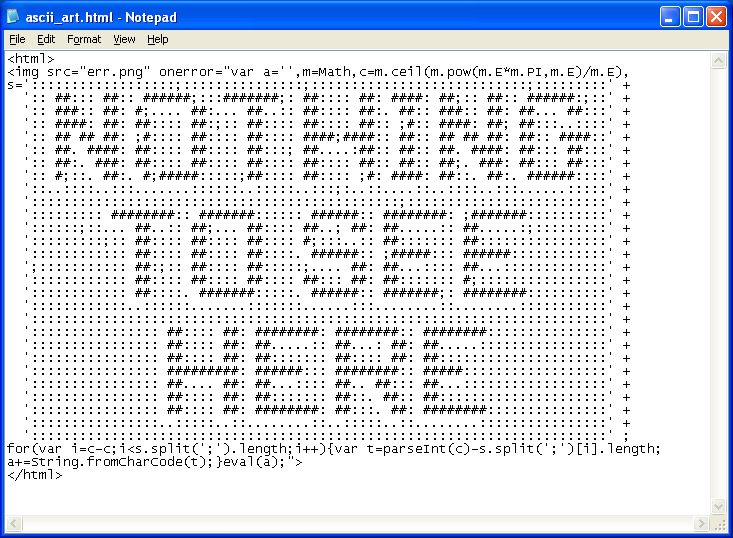
This method of data obfuscation was designed to be easily accessible to users without a deep understanding of cryptic knowledge or the tools to do so. Basically, an algorithmic-frustrating queue is out of the ordinary for a known advertising ID (you, the user). A project developed by Nissenbaum called "TrackMeNot" is a simple Firefox extension that will periodically make false searches in order confuse tracking algorithms.
Brunto, co-creator of TrackMeNot, says that the inspiration for this extension is similar to an old military trick of confusing a radar of pinpointing where an airplane's location is. Rather than covering up the plane's location, pilots would drop out hundreds of these aluminum sheets and the radar would pick these sheets up on the radar and there would be so many dots, the operator would not know who or where the airplane was.
The same thing can be applied to users and algorithms. Rather than trying to conceal a single "dot" it is much easier and just as effective to create hundreds of dots that confuse the operator or algorithm. All of these false dots create a "fog" and the user can freely navigate around this cloud without being accurately traced.
"Brunton and Nissenbaum also see a social purpose in obfuscation, born out of a responsibility that those who have "nothing to hide" owe to those who might: “to conceal, muddle, and obfuscate our activities precisely to confuse the construction of normalcy that can be used to identify the abnormal and secretive.” Uploading or appearing to upload non-sensitive material to a whistleblowing website, for instance, could help bury the identity of a leaker in noise, which “helps protect the one who really needs it.""
(Pangburn, DJ. VICE Motherboard. https://www.vice.com/en_us/article/yp3ex7/obfuscate-yourself-nissenbaum-brunton)
This actually brings up questions in the "Programmers Code Of Ethics" about the deliberate pollution of data flow that may compromise its integrity. Brunton and Nissenbaum both concisely state that “[d]ata pollution is unethical only when the integrity of the data flow or data set in question is ethically required.” In the case of advertisement and metadata, the value of data is all in favor of the company and may go against the user's interests.
Overwhelm "the system" by putting everybody on "the list."
 Source: http://thelancet.com/
Source: http://thelancet.com/
A more comical way to "defeat the system" is, instead of hiding from surveillance, make sure that you make every bell and whistle go off on internet monitoring agencies. This takes a massive group effort, though. The thinking goes back to the telephone infrastructure – the service reaches everyone, but if everyone wanted to pick up the phone and call someone at the same time, the whole service would go down. Surveillance algorithms and tracking work the same way. If everybody is on "the list" the algorithmic monitoring system is unable to handle the traffic.
Reddit user /u/K_Lobstah created a website "Ruin My Search History" that runs a script of questionable searches and is sure to put you on some kind of list somewhere. It is important to remember that searching for anything is completely legal, it is only when users access material it becomes a question of legality. The searches this script runs is pretty mild in the grand scheme of things, but reading people's reactions and thoughts to this program is quite entertaining.
The searches almost tell a story of a distressed man that goes on a Google search binge that starts with the question "why are my thumbs uneven" and leads him to joining ISIS and Googling "Bing".
Some other searches include:
- "am I lack toast and tolerant"
- "your youre difference"
- "ways to kill someone hypothetically"
- "how to delete search history in browser"
- "syria hotels with pool"
The whole Reddit thread on this website, people's commentary, and people's reaction can be found HERE (Some explicit language).
There was a lot of controversy when this post was created, because some people clicked the "Ruin My History" button and the search results really scared them. Like I and others have pointed out, a search for something is never illegal; only accessing the material can be tried. This lighthearted joke (for those well rounded in internet knowledge, at least) is a statement on how scared people are to search online because of the known fact they are constantly monitored.


Comment